Sharpen your Security using AWS Security Hub

AWS Security Hub is a Cloud Security Posture Management (CSPM) that automates the identification and remediation of risks across cloud infrastructures like IaaS, SaaS, and PaaS. It improves your security position with automated security best practice checks powered by AWS Config rules and automated integrations with dozens of AWS services and partner products.

Why Security Hub?
Pre-built dashboard offered by Security Hub helps you to organize and prioritize any issues or alerts on your AWS environment discovered from the security checks. The growing popularity of Amazon Web Services (AWS) triggered the importance of AWS Security Hub for businesses across the globe. Amazon enables the data collection from AWS OR third-party services for your business so that you don’t need to deal with time-consuming data processing activity.
According to Statista, Amazon Web Services (AWS) continues to lead USD 180 Billion global cloud infrastructure with 33% of the market share at the beginning of the year 2022.
Here are some of the top benefits of using Amazon Security Hub for businesses like yours.
Quick and Accurate Security Findings:
With Amazon Security Hub, you can reduce the effort needed to collect and prioritize security findings across accounts with integrated AWS services and AWS partner products. It enables you to find data using standard finding formats which leads to the elimination of the need to manage and find data from multiple sources. The platform itself correlates the finding across providers to help you prioritize the most critical security issues.
Enables Best Security Practices and Standards:
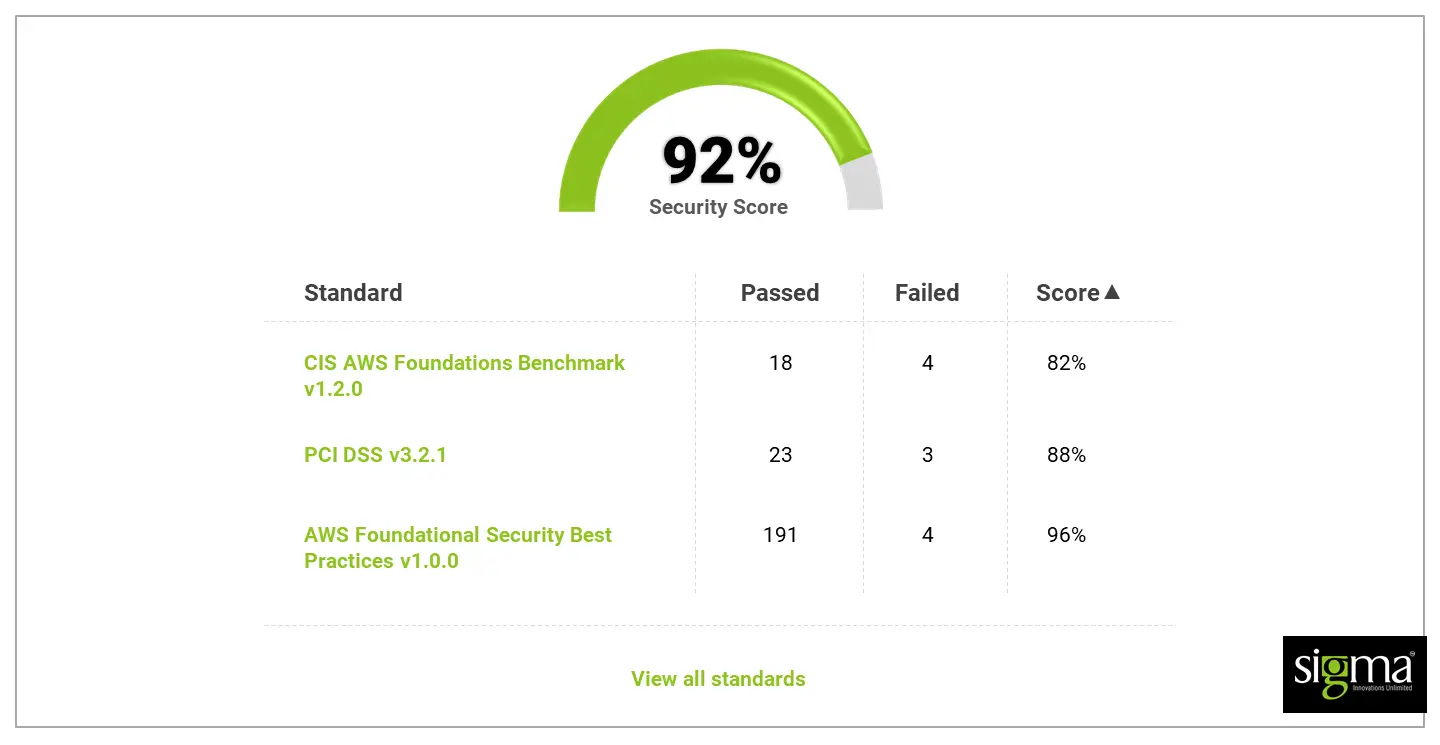
Amazon Security Hub itself is capable of running account-level configuration and security checks based on best practices and industry standards continuously. The platform offers the result of these checks as a readiness score, and recognizes specific accounts & resources that require immediate attention.
Provides Consolidated View of Findings:
It consolidates the security findings across the accounts and products for your business and displays amazing outcomes on the Security Hub console which allows you to visualize the overall security status to spot trends, identify potential issues, and take the necessary remediation steps in real-time.
Power to Automate Remediation:
The Amazon Security Hub also enables you to integrate with Amazon EventBridge at ease. With this integration, you can automate remediation of specific findings and define custom actions needed when a finding is received.
In nutshell, Security Hub enables you to check your environment against AWS security industry standards and best practices and take advantage of PCI-DSS and CIS (Center for Internet Security) built-in automatic checks.
How to Perform Security Hub and AWS Services Integration?
You might not get surprised if we tell you integrating Security Hub with AWS services is very easy if you know how to perform this integration with perfection. Each and every AWS security tools facilitate seamless integration with Security Hub. In order to help you and your business with this aspect we have compiled the list of AWS services to get integrated with:
Amazon GuardDuty:
Amazon GuradDuty is a threat detecting service offered by AWS services that continuously monitors your AWS accounts, s3 Bucket, and workloads for malicious activity in order to deliver detailed security findings for visibility and remediation.
Amazon Macie:
In case you are looking for fully managed data security and data privacy services with the power of machine learning and pattern matching features the Amazon Macie is the one. It helps you discover and protect your sensitive and confidential data in AWS.
Amazon Inspector:
Amazon Inspector is the best-in-class vulnerability management service that AWS offers. It continuously scans your AWS workloads for vulnerabilities and automatically discovers & scans Amazon EC2 instances and container images residing in Amazon Elastic Container Registry (Amazon ECR) for software vulnerabilities and unintended network exposure.
IAM Access Analyzer:
If you are in need of resource identification within your organization and accounts such as Amazon S3 buckets or IAM roles that are shared with an external entity, then IAM Access Analyzer from AWS can help you do so. It enables you to identify unintended access to your resources and data which may lead to a security risk for your business.
Amazon CloudWatch and CloudWatch Events:
This feature by AWS delivers a real-time stream of system events that describes alterations in the Amazon Webs Services (AWS) resources. The CloudWatch Events enables you to get aware of the operational changes as they occur, and respond to such changes in order to take corrective actions as necessary in near real-time by sending messages to respond to the environment, activating functions, making changes, and capturing state information.
AWS Firewall Manager:
Using AWS Firewall Manager allows you to centrally configure and manage web application firewall rules and security groups across the multiple AWS accounts and applications. The creation of new applications makes it easy for you to bring new applications and resources into compliance by enforcing common sets of security rules to create security policies, and enforce them in a consistent and hierarchical manner across your entire infrastructure, from a central administrator account.
Best Security Hub third-party tool integration
AWS Security Hub also empowers businesses with automatically aggregate security findings data from supported AWS Partner security solutions to facilitate a comprehensive view of security and compliance across your AWS environment by integrating with many different third-party tools.
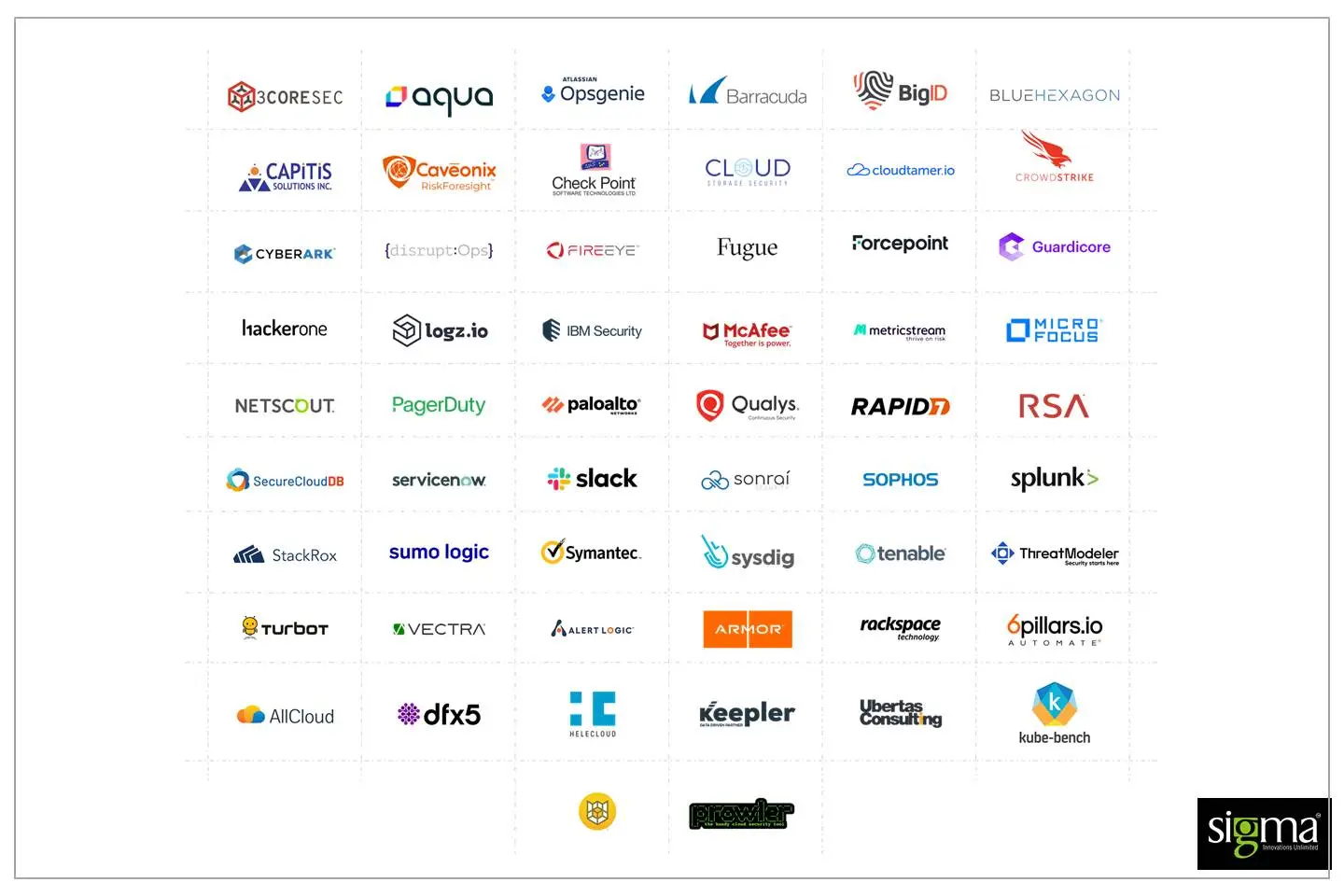
To explore more details about the nature of these third-party integrations and find the best fit for your business needs, you can check them out on the official AWS page: integrated AWS Partner Network (APN) security solutions.
Top Available security standards and best practices checks:
For your eCommerce business, you might not find the right security standards and best practice checks as an exciting factors to consider, but the truth is they are very critical for your success. AWS Security Hub offers you the flexibility to choose the best security standards that suits your business needs. It also provides you with a set of controls to determine compliance with regulatory frameworks and industry best practices.
Here are the three automated checks you can enable at this moment:
AWS Foundational Security Best Practices
The standard is a set of automated security checks to detect whether your AWS accounts and deployed resources are aligned with security best practices or not. The AWS Foundational Security Best Practices standard is defined by AWS security experts and curates a set of controls to improve your security posture in AWS, and covers AWS’s most popular and foundational services.
AWS Security Hub CIS Benchmark
This standard is widely used across industries and is accessible to businesses of all sizes. The Center for Internet Security standard is used to perform strategic-level assessments of your security program. The CIS has published a benchmark with general security guidelines for AWS which enables AWS Security Hub standard to automatically check your compliance readiness against a subset of CIS requirements.
This includes things like:
- Avoid the use of the “root” account
- Ensure credentials unused for 90 days or more are disabled
- Ensure the IAM password policy requires a minimum length of 14 or greater
- Ensure MFA is enabled for the “root” account
- Ensure no security groups allow ingress from 0.0.0.0/0 to port 22
- Ensure rotation for customer-created KMS keys is enabled
To get a detailed insight into CIS requirements, you can also go through the official website of CIS AWS Foundations Benchmark controls.
Payment Card Industry Data Security Standard (PCI DSS)
The PCI data security standard is a set of checks related to credit card payments that you need to adhere to if you’re handling anything to do with credit cards. In order to find more information about it, please visit the AWS official document on PCI DSS.
How to configure Security Hub?
To configure Security Hub you must enable resource recording in AWS Config first. Since the charges are different for the AWS Config from Security Hub, you must visit Config pricing for more information.
Follow the below-mentioned steps to configure Security Hub:
Step 01: Open the AWS Config console.
Step 02: You should see an option to choose a 1-click setup to launch AWS Config based on AWS best practices.

Step 03: In Review, click on “Confirm”.
For some of the security checks, you will also need AWS CloudTrail. In the case of other AWS services, you can use multiple ways to enable Security Hub, but we will suggest choosing the one that suits you the most.
Enable Security Hub in AWS Management Console:
Step 01: Sign in to the Security Hub console.
Step 02: Choose “Go to Security Hub”.
Step 03: Choose “Security standards”. You can enable or disable a standard at any time after enabling Security Hub.
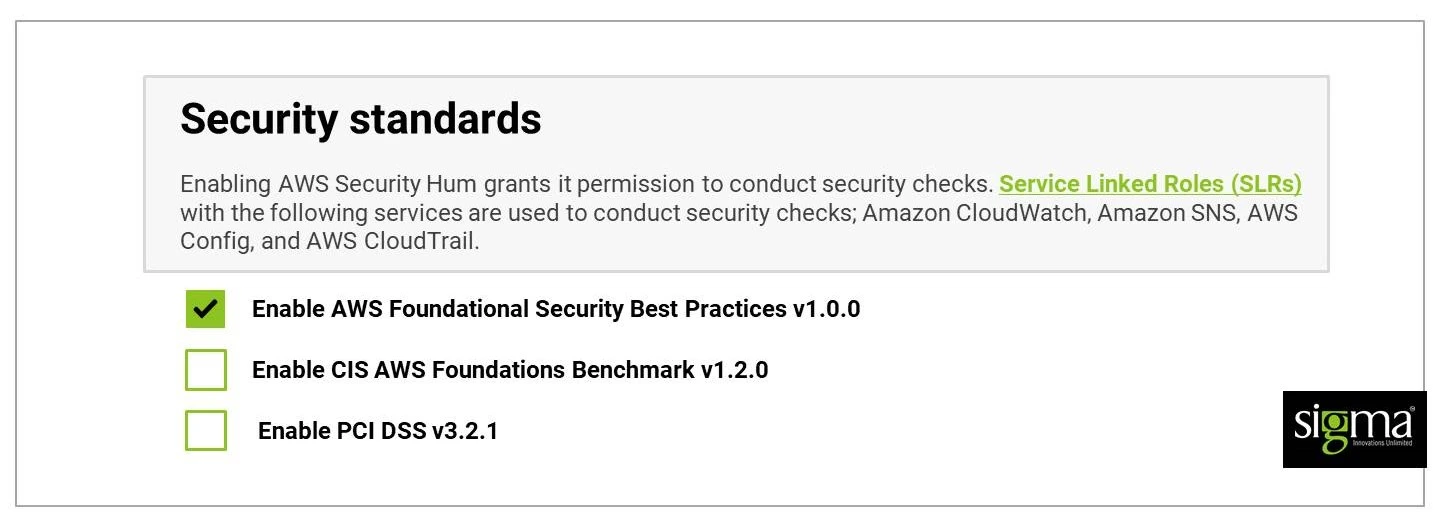
Step 04: Choose “Enable” Security Hub.
Security Hub pricing
Looking at the benefits your business can get from AWS Security Hub, you will certainly be interested in knowing its pricing. As we have already disclosed that Security Hub’s security checks leverage items recorded by AWS Config and AWS Config is priced separately from Security Hub, you can visit and find AWS Config pricing for more information.
AWS Security Hub offers usage (cost) information in its Settings to help you understand how your monthly billing estimates will look like and what all components of AWS Security Hub are contributing to your bill. Also, your AWS account will automatically get enrolled in a 30-day Security Hub free trial if you enable AWS Security Hub for the first time.
Conclusion:
AWS Security Hub enables automated integrations with dozens of AWS services and partner products for your business and also helps you improve your security posture with automated security best practice checks powered by AWS Config rules. Also, AWS security and compliance capabilities implement effective practices to safeguard your organization’s data in AWS cloud storage and are well suited to help you review the SEC OCIE observations.
Planning to enhance your organization’s security on the cloud with a trusted technology partner? Feel free to reach us out at [email protected] to discuss further how we can help your business to scale at speed within a secured cloud environment.